RidgeBot – Automated Penetration Testing Tool
RidgeBot – Automated Penetration Testing Tool
Automated Pentest Robot to Achieve Enterprise Risk-Based Vulnerability Management
Available on backorder
SKU RBCLOUD-1YR Category IT Security Software
Description
RidgeBot – Automated Penetration Testing Tool
Automated Pentest Robot to Achieve Enterprise Risk-Based Vulnerability Management
Smart Finger Printing and Smart Webcrawling
RidgeBot® automatically crawls or scans the specified IT infrastructure to identify and document a broad type of assets and the attack surfaces of those assets
- 5600 OS fingerprints/11000 Service fingerprints
- Asset Types Supported: IPs, Domains, Hosts, OS, Apps, Websites, Plugins, Network and IoT Devices
The following technologies but not limited to are included in this stage:
- Crawling, URL brute force, domain name resolution, subdomain brute-force, associated domain extraction, neighboring site inspection, web fingerprint, host fingerprint, system fingerprint, active host inspection, email extraction, login entries discovery
Support all major web frameworks
- WordPress
- PHP/SQL
- VUE/React
- JavaScript
Ridgebrain expert & Vulnerability Mining
By leveraging the Asset Profiling results, RidgeBot will examine the assets and attack surfaces against its vulnerability knowledge base, discover all potential vulnerabilities to exploit:
- Web Applications
- Host/Database Servers
- Weak Credentials
- 3rd Party Framework vulnerabilities
The following techniques are used during the vulnerability mining process:
- Weakness discovering: Identify possible weak links on the attack surface and check for vulnerabilities based on the intelligent decision system such as the expert models and RidgeBot brains.
- Vulnerability scanning: Access and test the target system by using packet generated by an automatic tool and the payload provided by the attack component, vector engine etc., and the returned results are checked to determine whether there are vulnerabilities that can be exploited.
Auto Exploitation
RidgeBot has an extensive knowledge base, the customer can either choose the exploits based on the test goal and target; or choose to use full scan and have RidgeBot conduct auto-exploitation.
- 2B threat intelligence
- 150K exploit database
- 6000 build-in POC exploits
The following techniques are used during the vulnerability exploit process:
- Internal attack: Launch attacks from inside of Enterprise network with customer’s permission, focusing on exploiting vulnerabilities discovered on local network and systems.
- External attack: Launch attacks from outside Enterprise networks towards publicly accessible assets such as organizations’ websites, file shares, or services hosted in public cloud/CDN
- Lateral Movement: After gaining a permission to the target host, use the host as a pivot to further exploit vulnerabilities and gain access to other parts of the system.
Realtime Attack Visualisation
Auto Topology Drawing
- Shows relationships of assets and attack surfaces
- Map out vulnerabilities and risks
Full Attack Path Visibility
- Track the attack source and show the attack details
Show the real-time actions on the dashboard
- Discover
- Scan
- Exploit
Risk Based Assessment
Health Score: Rank and remediate vulnerabilities based on risk assessment
- Detailed and specific ranking of the most harmful vulnerabilities
- Visualize the kill-chain
- Comprehensive health score based on the weighted evaluation
Kill Chain Visualization: A Risk is defined as “An exploit with a completed kill-chain accomplished”
- Exploit attempts launched toward each exploitable vulnerability, only those accomplished the whole kill-chain will be documented in the final report.
- Four types of risks shown in the final report
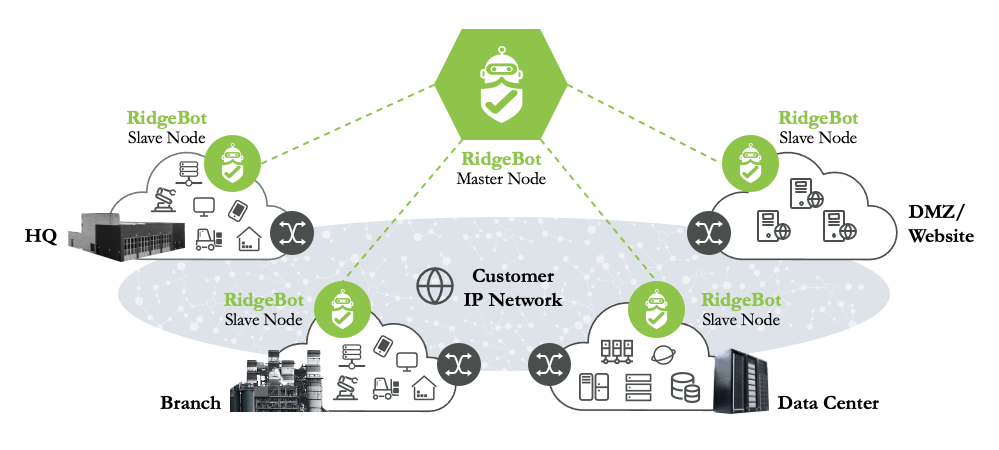
Distributed Architecture for large scale Infrastructure
Recommendation: One RidgeBot Slave Node per 500 target systems (or per subnet)